Total Data Protection
Enterprise Class Security Solutions for SMB
Promotional onsite service charge of $49/per visit to solve your IT Issues
Applicable to SME only
Contact us via email : sales@anyware.com.sg

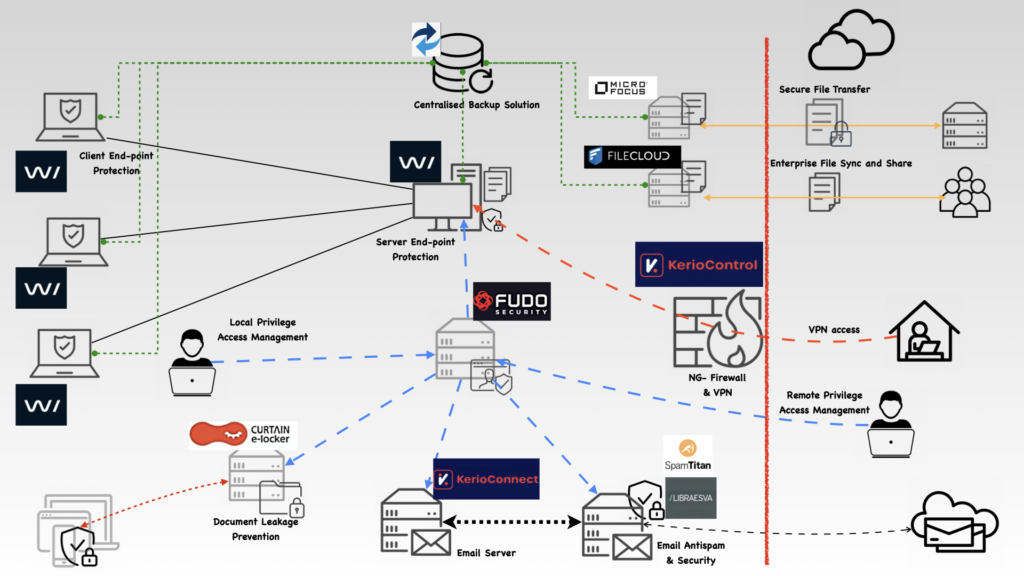
Safe Guard your DATA and Reputation
Anyware IT solutions prides itself in finding excellent security solutions which are not deep on your pockets. Our expertise had been ensuring our customers data and network is secured holistically and not find themselves an easy target for hackers, scammers and data thief.
You already have an in-house IT staff or your are being serviced Outsourced Vendor…. No Problem At All… We can still help you enhance your security coverage and help you identify the areas which were overlooked. If possible our recommendation can reduce your IT expenditure by big margin.
Remember your data is critical to your operation and leakage of it is not pleasant to your reputation. We offer non-obligatory consultancy service, we do it over web-session or onsite visit.
Our Services
IT Support Package
We’ve Comprehensive and Affordable IT support Packages catering to your needs by Well Trained Professionals with years of experience.
Premium Support Package
$1800/month
- 20 Hours Onsite Support Hours
- 2 Hrs Response Time
- Support Covers Desktop and Server OS/Software/ Hardware Issues
- Unlimited Email/Chat Support (9-6 Business Days)
- 10 Desktop + 1 Server Backup Client + 1TB Cloud Storage
- Remote Assistance
- First consultancy service free
- Free IT Security Review
Standard Support Package
$1200/month $600/month
Price after applying promotional discount of 50%
- 10 Hours Onsite Support Hours
- Response By Next Business Day
- Support Covers Desktop OS/Software/Hardware Issues
- 50 Email/Chat Support/Mnth (9-6 Business Days)
- 5 Desktop Backup Clients + 500GB Cloud Storage
- Remote Assistance
- First consultancy service free
- Free IT Security Review
Our Solutions Portfolio
Some of the amazing Products which form our Solutions Portfolio
Let’s Get in Touch for Free Consultancy
We offer free non obligatory consultancy service, all we care is how we can help better protect your network and data. Do not hesitate to contact us..
Testimonials
Excellent product and back up service from the good people at Anyware IT Solutions. Highly recommend 🙂
Woon Kee Yang
Yu Fish Pte Ltd
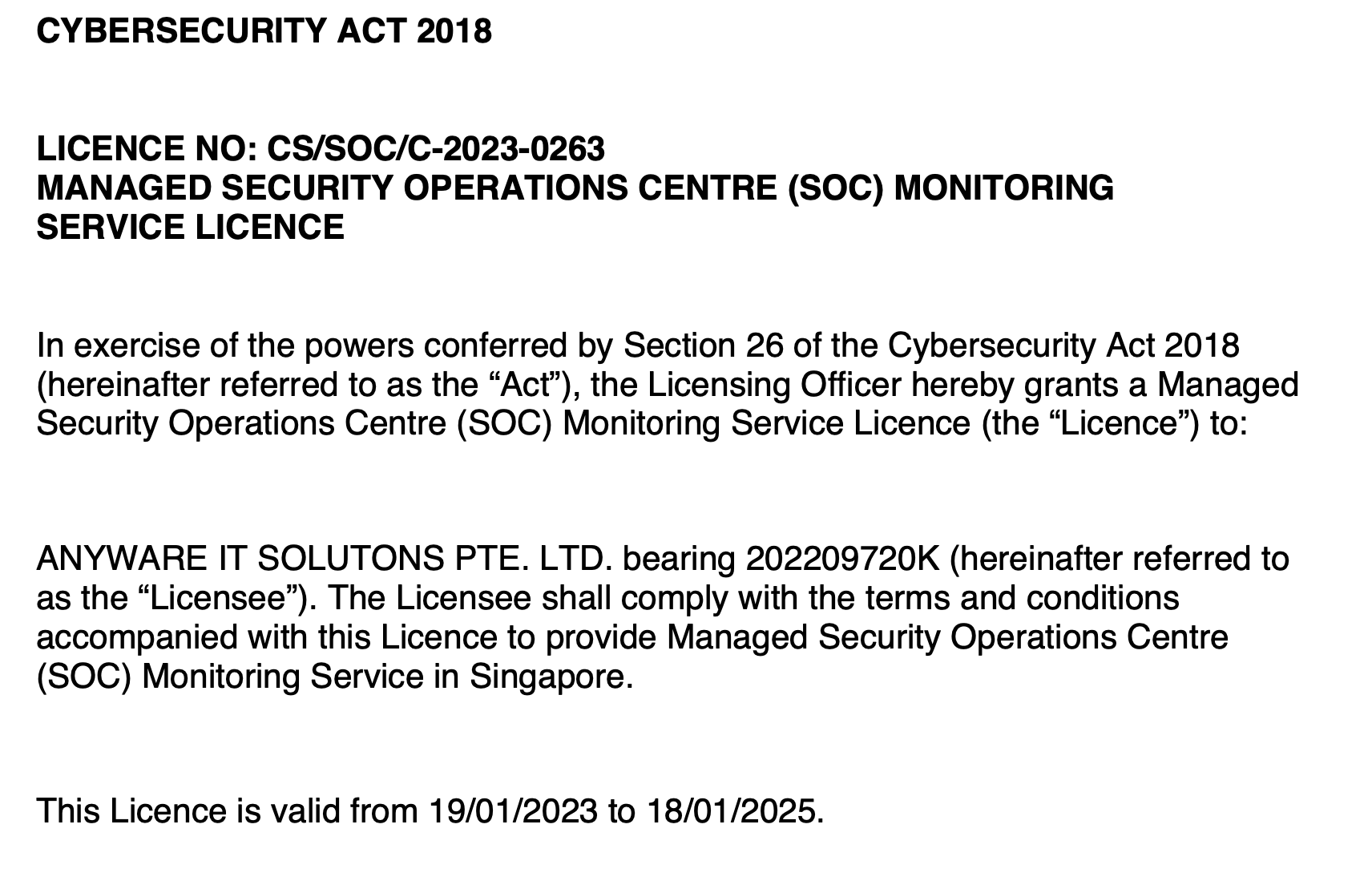
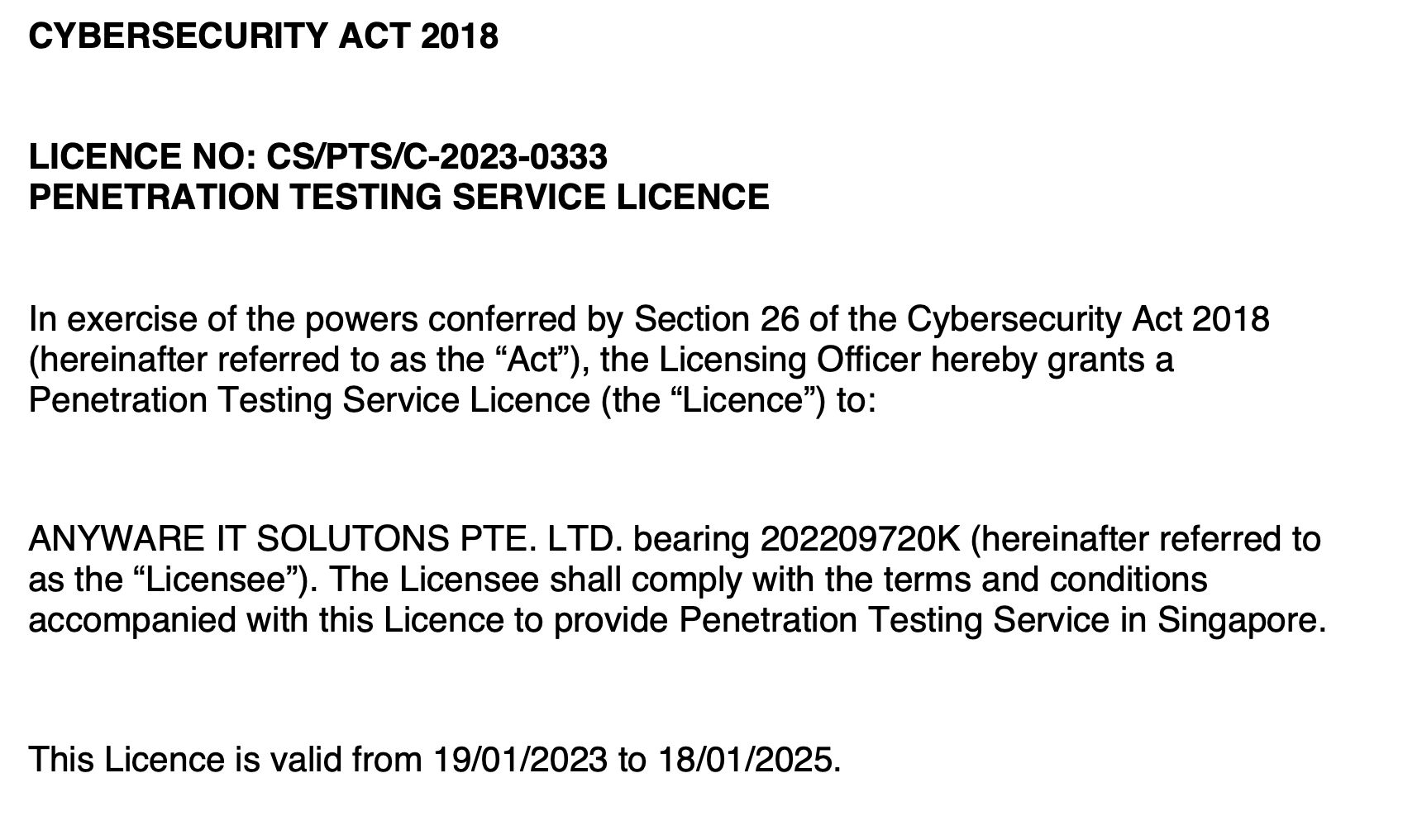
Accreditation
- 6 HIDDEN THREATS IN CORPORATE EMAIL
 The best place to hide a book is in a library. The most ideal place to hide a leaf is in the forest. And the best way to hide a… Read more: 6 HIDDEN THREATS IN CORPORATE EMAIL
The best place to hide a book is in a library. The most ideal place to hide a leaf is in the forest. And the best way to hide a… Read more: 6 HIDDEN THREATS IN CORPORATE EMAIL - EMAIL ACCOUNT TAKEOVER:BEST PRACTICES FOR REDUCING RISK
 How account takeovers work Account takeover – the criminal use of compromised online accounts – has the potential to be immensely profitable. Hackers steal credentials from individuals (see phishing) or target an… Read more: EMAIL ACCOUNT TAKEOVER:BEST PRACTICES FOR REDUCING RISK
How account takeovers work Account takeover – the criminal use of compromised online accounts – has the potential to be immensely profitable. Hackers steal credentials from individuals (see phishing) or target an… Read more: EMAIL ACCOUNT TAKEOVER:BEST PRACTICES FOR REDUCING RISK - Big Head Ransomware
 TrendMicro analyze the technical details of a new ransomware family named Big Head. Big Head, which came out in May 2023, has at least three variants, all designed to encrypt… Read more: Big Head Ransomware
TrendMicro analyze the technical details of a new ransomware family named Big Head. Big Head, which came out in May 2023, has at least three variants, all designed to encrypt… Read more: Big Head Ransomware
-
6 HIDDEN THREATS IN CORPORATE EMAIL

The best place to hide a book is in a library. The most ideal place to hide a leaf is in the forest. And the best way to hide a suspicious email? In plain sight. Email security fraud is now so common that most internet users are now aware of basic hacker tricks, such as…
-
EMAIL ACCOUNT TAKEOVER:BEST PRACTICES FOR REDUCING RISK

How account takeovers work Account takeover – the criminal use of compromised online accounts – has the potential to be immensely profitable. Hackers steal credentials from individuals (see phishing) or target an entire organization using bots. They then use these stolen credentials to take ownership of the compromised accounts or sell credentials lists to other cybercriminals. Whoever…
-
Apple “My Photo Stream” is shutting down

Apple’s “My Photo Stream” service is shutting its door on July 26, 2023. Most Apple users who are reliant on this FREE feature would be forced to pay for the premium iCloud Photo service. What is My Photo Stream: It is a free service that uploads the last 30 days of images (up to 1,000) to iCloud,…