Lightning Framework is a new undetected ‘Swiss Army Knife’-like Linux malware that has modular plugins and the ability to install rootkits. The framework has both passive and active capabilities for communication with the threat actor, including opening up SSH on an infected machine, and a polymorphic malleable command and control configuration. The framework consists of […]
Data Leak: What and How to Prevent
A data leak is an unauthorized data transfer from within a company to a third party. Individuals, companies, and government agencies experience financial and reputational loss if unauthorized parties get access to their sensitive data. All businesses benefit from monitoring cybersecurity risks and taking appropriate steps to prevent data loss and theft. In this article, […]
Your Complete Guide to Digital Workplace Solutions
A digital workplace is a virtual platform designed to streamline everyday work and improve employees’ efficiency, collaboration, and morale. It’s a central hub that extends the physical office workspace and allows employees to work without being bound to a single location. Employees use digital workplace technologies to streamline business operations, communicate securely, and share ideas […]
VMs vs Containers : Which should you Pick
If you’re looking to improve computer performance, the list narrows down to two notable inventions: virtualization and containerization. Both methods have allowed IT professionals to benefit from the physical hardware running on a server. The goal is to use the same resources but run different operating systems. The question I’ll be answering in this article is: which […]
ABCsoup: The Malicious Adware Extension with 350 Variants
Recently, Zimperium discovered and began monitoring the growth of a wide range of malicious browser extensions with the same extension ID as Google Translate. This family, codenamed ABCsoup, targets three popular browsers: Google Chrome, Opera, and Firefox. https://blog.zimperium.com/abc-soup-the-malicious-adware-extension-with-350-variants/
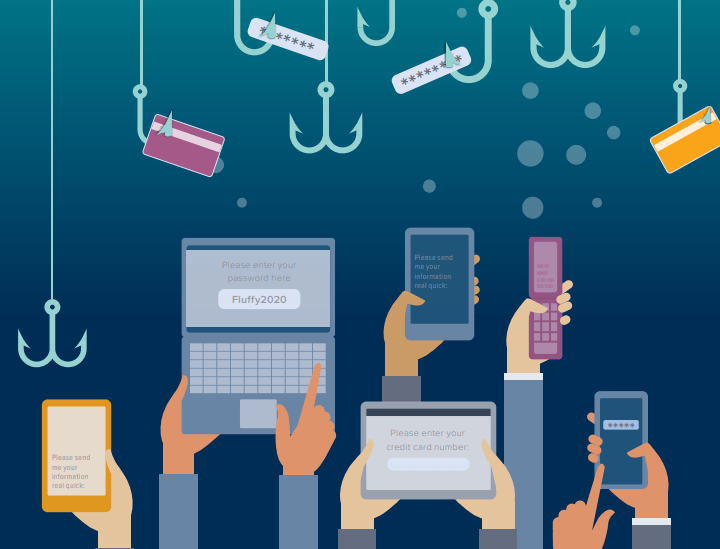
RansomWare : BlackByte
BlackByte is a ransomware family that has been building a name for itself since 2021. Like its contemporaries, it has gone after critical infrastructure for a higher chance of a getting a payout. Blackbyte Initial versions used symmetric keys, it has multiple variants, archives files using WinRAR, uses trojanized legitimate tools, and involves phishing emails […]
Tips and Tutorials
A good way to get your head around any technology area is to begin by reading a well-crafted article on the subject that starts with “What is…?” Here are a few of our favorite what-is guides from our TechGenix website: What Is Network Orchestration? What Is Virtualization-Based Security (VBS)? What Is Network Segmentation? What Is a Digital […]
Linux News
It used to be that Microsoft attracted all the attention of malicious hackers. They seemed mostly happy to leave macOS and Linux alone for the most part. Not any more (Ars Technica). Will Microsoft’s growing footprint in the Linux/FOSS landscape cause the Black Hat community to up their targeting of Linux systems? What do you think? Open Source software […]
Interactive Phishing Mark II: Messenger Chatbot Leveraged in a New Facebook-Themed Spam
Facebook Messenger is one of the most popular messaging platform in the world, amassing 988 million monthly active users as of January 2022 according to Statista. One important feature of this platform is Messenger’s bot. Within the current digital landscape, chatbots are widely used by companies and individuals to connect with their customers online, and […]
Xiaomi puts a 1-inch camera sensor in their New Flagship Phone
Courtesy: Jacob Kastrenakes Xiaomi is introducing a trio of new smartphones today, and one of them comes with a pretty huge new feature: a 1-inch camera sensor, which is relatively giant for a smartphone. Everything about Xiaomi’s new flagship smartphone, the Mi 12S Ultra, is big. It has a 6.73-inch OLED display, a top-of-the-line Snapdragon 8 Plus […]
Smash-and-Grab: AstraLocker 2.0 Pushes Ransomware Direct from Office Docs
ReversingLabs recently discovered instances of the AstraLocker 2.0 malware distributed directly from Microsoft Word files used in phishing attacks. The “smash and grab” attack methodology as well as other features suggest the attacker behind this malware is low-skill and looking to cause disruption, compared with the more patient, methodical, and measured approach to compromises used […]
Spyware Vendor Targets Mobile Users
Google has been tracking the activities of commercial spyware vendors for years. Recently, RCS Labs, an Italian vendor, has been found to use a combination of tactics, including atypical drive-by downloads as initial infection vectors to target mobile users on both iOS and Android. Google has identified victims located in Italy and Kazakhstan. All campaigns […]
Rise of LNK (Shortcut files) Malware | McAfee Blog
A LNK file is a Windows Shortcut that serves as a pointer to open a file, folder, or application. LNK files are based on the Shell Link binary file format, which holds information used to access another data object. These files can be created manually using the standard right-click create shortcut option or sometimes they […]
Windows Tips and Tricks
How to Deploy Windows 10 (11) with PXE Network Boot? (Windows OS Hub) How to Create a Wi-Fi Hotspot on your Windows PC? (Windows OS Hub) How to Repair EFI/GPT Bootloader on Windows 10 or 11? (Windows OS Hub) How to replace your Windows 11 Start menu with a third-party app (ZDNet) How to install Microsoft Store apps and […]