The best place to hide a book is in a library. The most ideal place to hide a leaf is in the forest. And the best way to hide a suspicious email? In plain sight. Email security fraud is now so common that most internet users are now aware of basic hacker tricks, such as […]
EMAIL ACCOUNT TAKEOVER:BEST PRACTICES FOR REDUCING RISK
How account takeovers work Account takeover – the criminal use of compromised online accounts – has the potential to be immensely profitable. Hackers steal credentials from individuals (see phishing) or target an entire organization using bots. They then use these stolen credentials to take ownership of the compromised accounts or sell credentials lists to other cybercriminals. Whoever […]
Tips And Best Practices For Small Business Email Management
One of my friends, Janet, is a classic example of why you need email management in your business. She constantly receives hundreds of emails at work. One day, she had an important client presentation in the afternoon. But the client sent her an email the previous night rescheduling the meeting to the early morning instead. […]
Manually Creating Swap Partition
Continuing from this articles…https://anyware.com.sg/re-sizing-linux-storage/ What happened to Swap…. Creating Swap partition alone would not suffice that it would be used by the system; it has to be initialized and activated. To initialize: # mkswap /dev/sda5 To activate: # swapon /dev/sda5 When I recreated the partition I didn’t know about the above and this… New Swap […]
Re-Sizing Linux Storage
Continuing from this article https://anyware.com.sg/debian11-128mb/ While testing out the file server services; the storage space soon filled up. That’s when I realised I had provisioned only 16GB of Storage most likely I thought I’m won’t doing anything else besides sftp testing. So how exactly I increased the Storage size… There are couple of options in […]
Debian 11 on 128 MB RAM
Coming from Win 3.1 days, I can’t fathom what the craze with modern operating systems gobbling GBs of RAM. Therefore I took it on myself to find which modern OS can smoothly run with the least amount of RAM. So I set out some parameter the OS should server, like it should have the complete […]
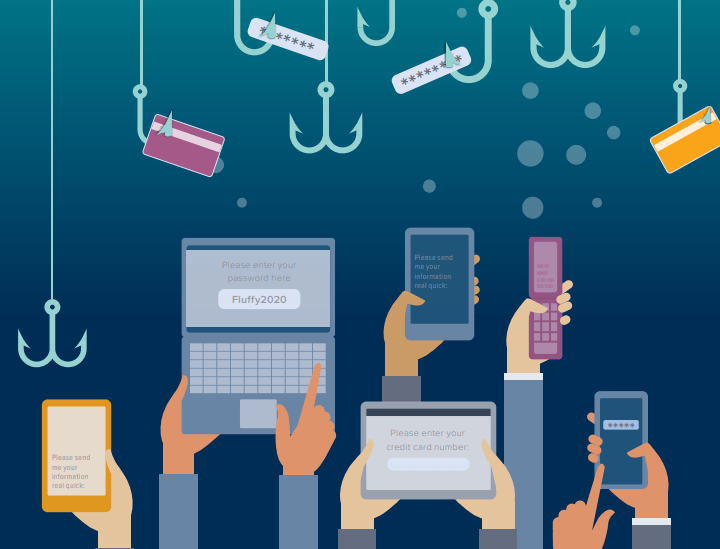
Phishing Activities in 2022
Phishing scams continue to plague the internet in 2022, more now than ever. This article explores the latest data and current trends and shows you how to avoid a phishing attack today. Cybercrime consultants have found over a million discrete phishing attacks perpetrated this year, which is up by 61% in the same time period in 2021. In […]
What is Advanced Malware Protection
Malware is a serious threat to both individuals and enterprises. It can compromise your sensitive data, disrupt operations, and even cause physical damage to computer systems. That’s not the end of the rope, though. If malware infects your system, it could severely damage your company’s reputation in the case of a data breach. In addition, […]
How to beef up Microsoft 365 Security
Microsoft has long used a shared responsibility model for its various cloud services, including Microsoft 365. The model states that Microsoft is responsible only for securing its cloud infrastructure. This means users are responsible for securing their data. But the problem is Microsoft 365 isn’t secure by default. So how do you get around this issue […]
Playing with Powershell Variables
Declaring a variable in PowerShell is usually a simple matter. Just specify the variable name, an equal sign, and the value you want to assign to the variable. Then PowerShell will do the rest. Despite this simplicity, you can make working with variables easier with a few extra tricks. For instance, you can define constants and […]
Guide to Cloud Data Security
Cloud storage is big, convenient, and here to stay. Unfortunately for many companies, cybercriminals are unrelenting in their effort to steal cloud data. For example, Cognyte, a cyber analytics firm, used third-party cloud software to store customer data. A misconfiguration in their cloud data security left one of their databases unsecured. As a result, criminals […]
Why are Network Management Solution Important
The network management solution (NMS) market contains many products that claim to offer the best experience and network security. To this end, choosing a solution that meets your needs can be challenging. One of the biggest challenges has to do with trusting these solutions. Are they safe? Are they reliable? Remember that you need to keep your network […]
What are Advanced Persistent Threats(APT)
Cybercriminals often use an advanced persistent threat (APT) to sustain surveillance or attacks against targets. One of the most valuable assets in a business is its data. Cybercriminals use APTs to steal your information, including trade secrets and patents. Also, bad actors can use APTs to gain employee and client information for extortion or to […]
Essential Email Security Policies
Although the average person may not encounter a substantial amount of emails, businesses and people within these businesses use email every day. Unfortunately, cybercriminals often use this common messaging tool as an attack vector. In this year’s Cost of a Data Breach Report, phishing is the costliest initial attack vector, with an average of USD4.91 million. The […]
Why You Need Email Spam Filter
Unwanted communication, or email spam, is a common challenge for many businesses today. Cyberattackers often send mass emails to millions of email addresses they scraped from the internet. These emails usually have a sense of urgency, lucrative offers, or even mimic other genuine sites. However, the main motivation behind these emails is far more sinister. […]
5 Things to Consider When Assessing Your VM Density
Businesses try to get the most out of any capital expenditure to improve their bottom line. When it comes to virtualization, this means trying to get the highest possible return on their virtualization hardware investment. You can do this by increasing the number of virtual machines (VMs) hosted. The greater the number of VMs, the […]
Removing Uninstalled Software Data from Windows
It’s common for Windows users to uninstall applications from their computers. It’s pointless to keep applications on your disk if you no longer use them. Unfortunately, when you uninstall an application, some of its data may remain on the hard disk. To make matters worse, these application remnants sometimes contain sensitive data. In this article, […]
Should you Filter Websites at Workplace
Remote working and web-based services are contributing to the success of many businesses. Yet, dependence on an internet connection makes companies vulnerable to web-based threats. For example, malicious software enters corporate networks when employees browse the internet. Also, clicking and downloading files from anywhere online increases malware risks by 32%. But you can still ban certain […]
Simple Penetration Testing Guide
The number of cyberattacks is increasing alarmingly around the globe. Nowadays, cybercriminals target almost all companies despite their size or domain. This encourages companies to find a solution to secure their systems and confidential data. Thus, companies invest large capital and resources in penetration testing as their first line of defense. Penetration testing is an effective cybersecurity […]
Is CIFS still relevant ?
Protocols have guided server-client communications for a long time—and they’re a good way to send and receive data. But every protocol has various nuances. Therefore, you should know which protocol you want to use before setting up a network. Even with the advancement of technology, server-client protocols have remained constant. As such, many are 20 years […]