The Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Agency (CISA) are releasing this joint CSA to disseminate known CL0P ransomware IOCs and TTPs identified through FBI investigations as recently as June 2023. According to open source information, beginning on May 27, 2023, CL0P Ransomware Gang, also known as TA505, began exploiting […]
Royal Ransomware
Backed by threat actors from Conti, Royal ransomware is poised to wreak havoc in the threat landscape, starting strong by taking a spot among the most prolific ransomware groups within three months since it was first reported. Combining new and old techniques and quick evolution, it is likely to remain a big player in the […]
Withsecure has developed Ransomware undo tech
Ransomware attacks have plagued organizations for the past several years, inflicting considerable financial losses. To help organizations manage ransomware and other threats, WithSecure™ (formerly known as F-Secure Business) has developed a new technology that can essentially undo the damage malware can cause. The technology, called Activity Monitor, was developed to make the capabilities of a sandbox […]
GlobeImposter Malware’s latest campagin
Since 2017, campaigns delivering GlobeImposter have continued to proliferate even though the ransomware has only evolved slightly. GlobeImposter is most often delivered via phishing email as an attachment or a link to a malicious attachment. The payloads are typically distributed via 7zip or traditional zip file archives. The archives often include a JavaScript (.js) file […]
Ransomware Attacks on Critical Infrastructure Fund DPRK Malicious Cyber Activities
The United States National Security Agency (NSA), the U.S. Federal Bureau of Investigation (FBI), the U.S. Cybersecurity and Infrastructure Security Agency (CISA), the U.S. Department of Health and Human Services (HHS), the Republic of Korea (ROK) National Intelligence Service (NIS), and the ROK Defense Security Agency (DSA) are issuing this joint Cybersecurity Advisory (CSA) to […]
ProxyShellMiner Targets Windows Endpoints
Morphisec has recently identified a highly evasive malware campaign delivering ProxyShellMiner to Windows endpoints. As the name suggests, ProxyShellMiner exploits the ProxyShell vulnerabilities CVE-2021-34473 and CVE-2021-34523 in Windows Exchange servers for initial access and compromise of an organization to deliver crypto miners. After successfully breaching an Exchange server and obtaining control, the attackers use the […]
Cl0p ransomware variant targets Linux
SentinelLabs observed the first ELF variant of Cl0p (also known as Clop) ransomware variant targeting Linux systems on the 26th of December 2022. The new variant is similar to the Windows variant, using the same encryption method and similar process logic. While the Windows versions contain a hashing algorithm in order to avoid encrypting specific […]
ESXi : ransomware target
The Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) are releasing this joint Cybersecurity Advisory (CSA) in response to the ongoing ransomware campaign, known as “ESXiArgs.” Malicious actors may be exploiting known vulnerabilities in VMware ESXi servers that are likely running unpatched and out-of-service or out-of-date versions of VMware ESXi […]
Ransomware Group Targets Manufacturing Companies
Vice Society, which was initially reported to be exploiting the PrintNightmare vulnerability in their routines, have previously deployed ransomware variants such as Hello Kitty/Five Hands and Zeppelin (the group’s email has been in their ransom notes). More recently, Vice Society has been able to develop its own custom ransomware builder and adopt more robust encryption […]
LockBit Ransomware Group is Formidable
LockBit has claimed to have stolen 76 gigabytes worth of confidential data, including financial and IT records, certifications, and legal documents, in an attack on California’s Department of Finance. While officials aren’t divulging much information, the LockBit group gave the department until December 24 to meet its demands. Or else, it threatened to leak the department’s […]
Deconstructing Azov: Sophisticated Wiper
Azov first came to the attention of the information security community as a payload of the SmokeLoader botnet, commonly found in fake pirated software and crack sites. One thing that sets Azov apart from your garden-variety ransomware is its modification of certain 64-bit executables to execute its own code. The modification of executables is done […]
Cuba ransomware analysis by TredMicro
Trend Micro has observed a resurgence of Cuba ransomware activity in March and April 2022. It included a new variant that contained updates to the binary – particularly its downloader – that is believed to enhance efficiency, minimize unwanted system behavior, and even provide technical support to victims in case of negotiations. Cuba ransomware has […]
A New Wave Of Ransomware Campaigns: AXLocker, Octocrypt
Ransomware operators have a new tool, named AXLocker, which can encrypt several file types and make them completely unusable. Additionally, the ransomware steals Discord tokens from the victim’s machine and sends them to a separate Discord server ran by the threat actors (TAs) . Finally, the AXLocker ransomware shows a pop-up window that contains a […]
Actor Profile: DEV-0243 – from FakeUpdates to Ransomware
Executive summary The threat actor that Microsoft tracks as DEV-0243, which overlaps with activity tracked by the cyber intelligence industry as EvilCorp , is a Russia-based cybercriminal group that’s been active since June 2014. It was also notorious for one of its earliest malware campaigns – the Dridex banking trojan. DEV-0243 is also one of the first […]
Hive Ransomware
The Federal Bureau of Investigation (FBI), the Cybersecurity and Infrastructure Security Agency (CISA), and the Department of Health and Human Services (HHS) are releasing this joint CSA to disseminate known Hive IOCs and TTPs identified through FBI investigations as recently as November 2022. As of November 2022, Hive ransomware actors have victimized over 1,300 companies […]
Venus Ransomware Targets Remote Desktop Services
Threat actors behind the relatively new Venus Ransomware are hacking into publicly-exposed Remote Desktop services to encrypt Windows devices. Venus Ransomware appears to have begun operating in the middle of August 2022 and has since encrypted victims worldwide. However, there was another ransomware using the same encrypted file extension since 2021, but it is unclear […]
QNAP NAS devices affected by ransomware
Network hardware-maker QNAP is urging customers to update their network-attached storage devices immediately to protect them from a new wave of ongoing ransomware attacks that can destroy terabytes of data in a single stroke. Singapore-based QNAP said recently that it has identified a new campaign from a ransomware group known as DeadBolt. The attacks take aim at […]
Ransomware Developers are using Intermittent Encryption
Partially encrypting victims’ files improves ransomware speed and aids evasion. First seen in LockFile, the technique is now being widely adopted. Intermittent encryption is important to ransomware operators from two perspectives: Speed: Encryption can be a time-intensive process and time is crucial to ransomware operators – the faster they encrypt the victims’ files, the less […]
HavanaCrypt Ransomware Masquarading as Google Update
First observed June 2022 in the wild, HavanaCrypt Ransomware masquerades as a legitimate Google Chrome update with sophisticated anti-analysis techniques and other functionality that may be used for data exfiltration and privilege escalation since its lack of a ransom note renders it unprofitable for its author. HavanaCrypt leverages functionalities from the open-source password software KeePass […]
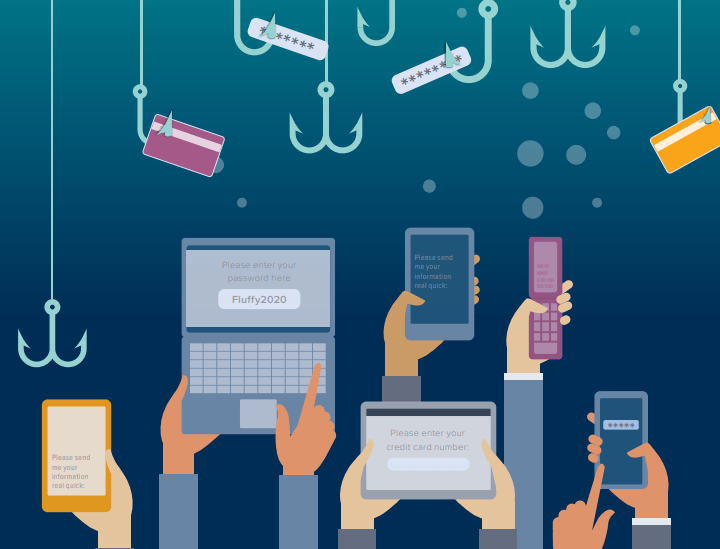
Ransomware as a Service
Do you know that a ransomware attack happens once every 11 seconds? Over the years, the frequency and intensity of these attacks have increased. This is due to the increased sophistication of cybercriminals and the easy availability of Ransomware as a Service (RaaS). Cybercriminals have also come up with ingenious ways to extort money from companies, and RaaS is […]